News
The Top 10 Worst Cyberattacks In The Middle East Revealed
Cybersecurity firm Positive Technologies has published a list covering the last 18 months of activity.

Over the last year and a half, the Middle East has witnessed a significant rise in cyberattacks, especially those posing a serious threat to organizations across the region.
Fedor Chunizhekov, Information Security Analyst at Positive Technologies, who compiled the list, explained, “The threat to the Middle East is very much real. Rapid advancement in technology and the growing independence on the internet means that attackers have novel and innovative ways to exploit vulnerabilities”.
Let’s check out some of the region’s worst attacks in the last 18 months:
Adalat Ali
In early 2022, Iranian hacktivists Adalat Ali successfully broadcast a 50-second message on streaming service Telewebion calling for further protests against the ruling Khamenei regime.
Bezeq And Cellcom DDoS Attack
In March 2022, a state of emergency was declared after a prolonged DDoS attack leading to Israeli government agencies, including the Ministry of Health, Internal Affairs, Prime Minister’s Office, and several major media outlets losing access to various services.
Public Address Systems In Palestine
In June 2022, public address systems in Jerusalem and Eilat were compromised by unnamed hackers, leading to false air raid sirens being broadcast for an hour.
Iranian Steel Plants Attack
Again in June 2022, an attack on three Iranian steel plants by hacktivist group Goneshke Darande disrupted processes leading to a liquid pig spillage resulting in a fire that halted production.
GamkenBot Scalper Bots
Attackers created bots that found and booked all available appointments using the Israeli booking service GamkenBot, before monetizing them and generally disrupting the service.
Cellebrite Data Breach
Israeli digital data firm Cellebrite was hacked to the tune of 1.7 TB of files in a massive data breach. The files contained all manner of proprietary backup software and other important information. No one has yet claimed responsibility for the attack.
Iranian News Agency Attack
A group of hacktivists known as Black Reward Team stole around 250 TB of confidential information from Iran’s state-run Fars News in November 2022. The group also gained access to CCTV footage.
Vice Society Attack On IKEA
Ransomware group Vice Society targeted IKEA in Morocco and Kuwait in November 2022. The outlets experienced a data breach that was thought to have been facilitated through phishing emails.
Pro-Palestine Attacks On Israeli Companies
In January, the hacktivist group Electronic Quds Force launched a campaign targeting Israeli chemical production companies. Messages sent to employees told them to “Leave employment and look for a new one”. The hackers also uploaded screenshots of automated control system interfaces on their Telegram channel, proving the plant was compromised.
Irrigation System Disruption
Farm irrigation systems and wastewater treatment in the Jordan Valley were targeted by what appears to have been OpIsrael, an anti-Israel hacktivist team. The attack was successful due to weak authentication and vulnerabilities in programmable controllers, allowing the attackers to gain remote access.
In light of such a severe spate of attacks, Positive Technologies urges companies to adopt the latest technologies and security techniques to safeguard data and networks against increasingly sophisticated hacking.
News
NVIDIA Puts GPT-5.5 Codex In Hands Of 10,000 Staff
The chipmaker has significantly expanded OpenAI’s latest model across teams from engineering to HR under tight internal controls.
NVIDIA has started rolling out OpenAI’s GPT-5.5 model through the Codex coding agent to more than 10,000 employees, extending the tool well beyond software teams and into core business functions.
The deployment covers engineering, product, legal, marketing, finance, sales, HR, operations and developer programs. Staff are using Codex for coding, internal research and routine knowledge work as companies test whether AI agents can move from demos to daily use.
GPT-5.5 is running on NVIDIA’s GB200 NVL72 rack-scale systems, linking OpenAI’s newest model directly to the chipmaker’s latest infrastructure push. NVIDIA said the systems cut cost per million tokens by 35 times and raise token output per second per megawatt by 50 times versus earlier generations.
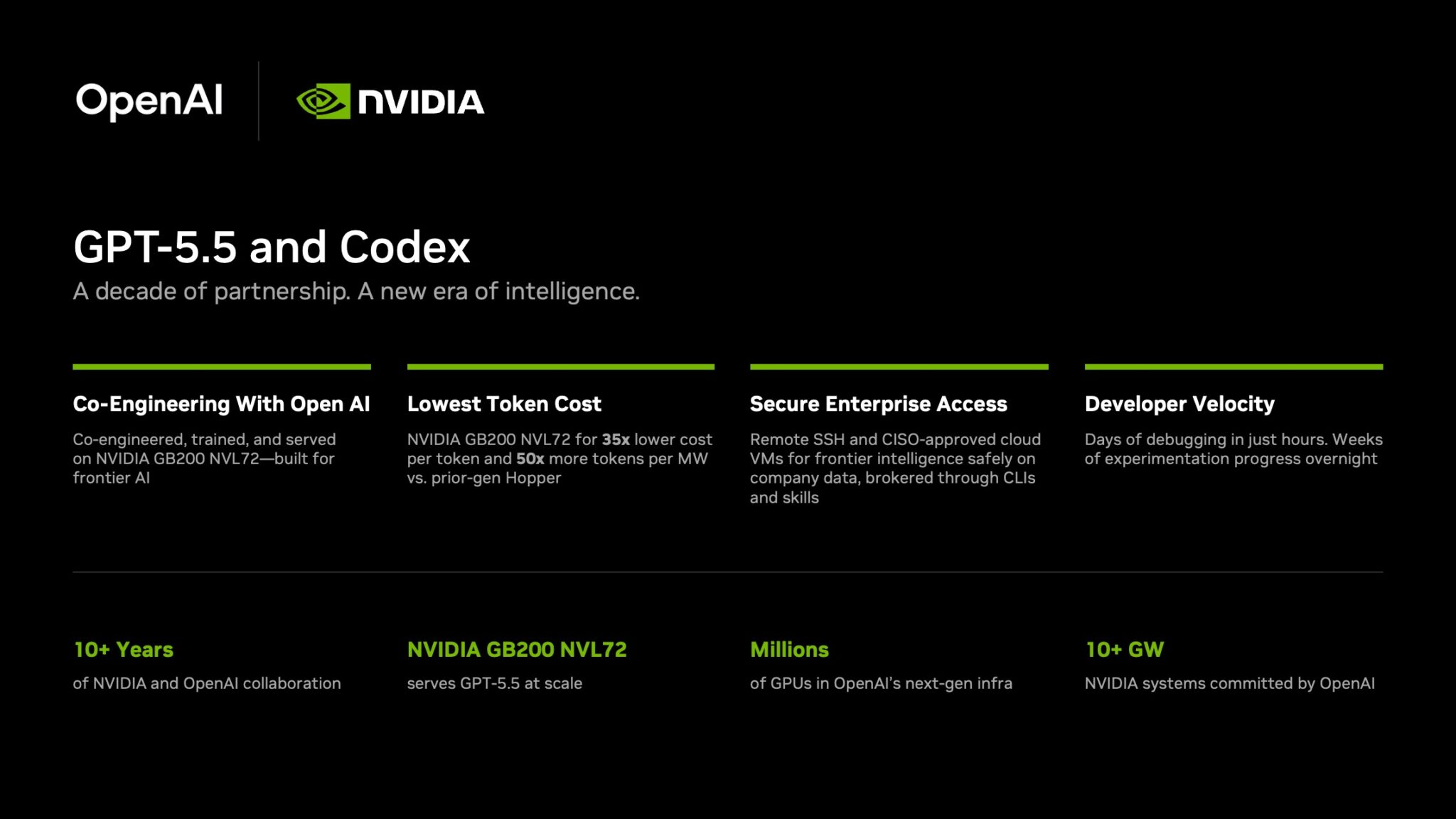
Inside the company, it says the effects are immediate. Debugging work that once took days is being finished in hours and experiments across large codebases that used to stretch over weeks are now handled overnight. Teams are also building features from natural-language prompts with fewer failed runs.
In a company-wide note urging staff to adopt the tool, CEO Jensen Huang wrote: “Let’s jump to lightspeed. Welcome to the age of AI.”
Security remains central to the rollout. Codex can connect through Secure Shell to approved cloud virtual machines, allowing agents to work with company data without moving it outside approved environments. NVIDIA said it assigned cloud VMs to employees so agents run in isolated sandboxes with full audit trails.
Also Read: Deezer Says AI Tracks Now Make Up 44% Of Uploads
The company added that the setup uses a zero-data-retention policy. Access to production systems is read-only through command-line tools and internal automation layers.
The move also highlights NVIDIA’s long relationship with OpenAI. NVIDIA said the partnership began in 2016, when Huang personally delivered the first DGX-1 AI supercomputer to OpenAI’s San Francisco office.
The two companies have since worked across hardware and model deployment. NVIDIA also said OpenAI plans to deploy more than 10 gigawatts of NVIDIA systems for future AI infrastructure.
For Gulf markets pouring money into sovereign AI and enterprise automation, the signal is clear: internal AI agents are moving from pilot phase to standard tooling.