News
100K+ Compromised ChatGPT Accounts Found On Dark Web
Egypt, Morocco, and Algeria top the list in the Middle Eastern region.

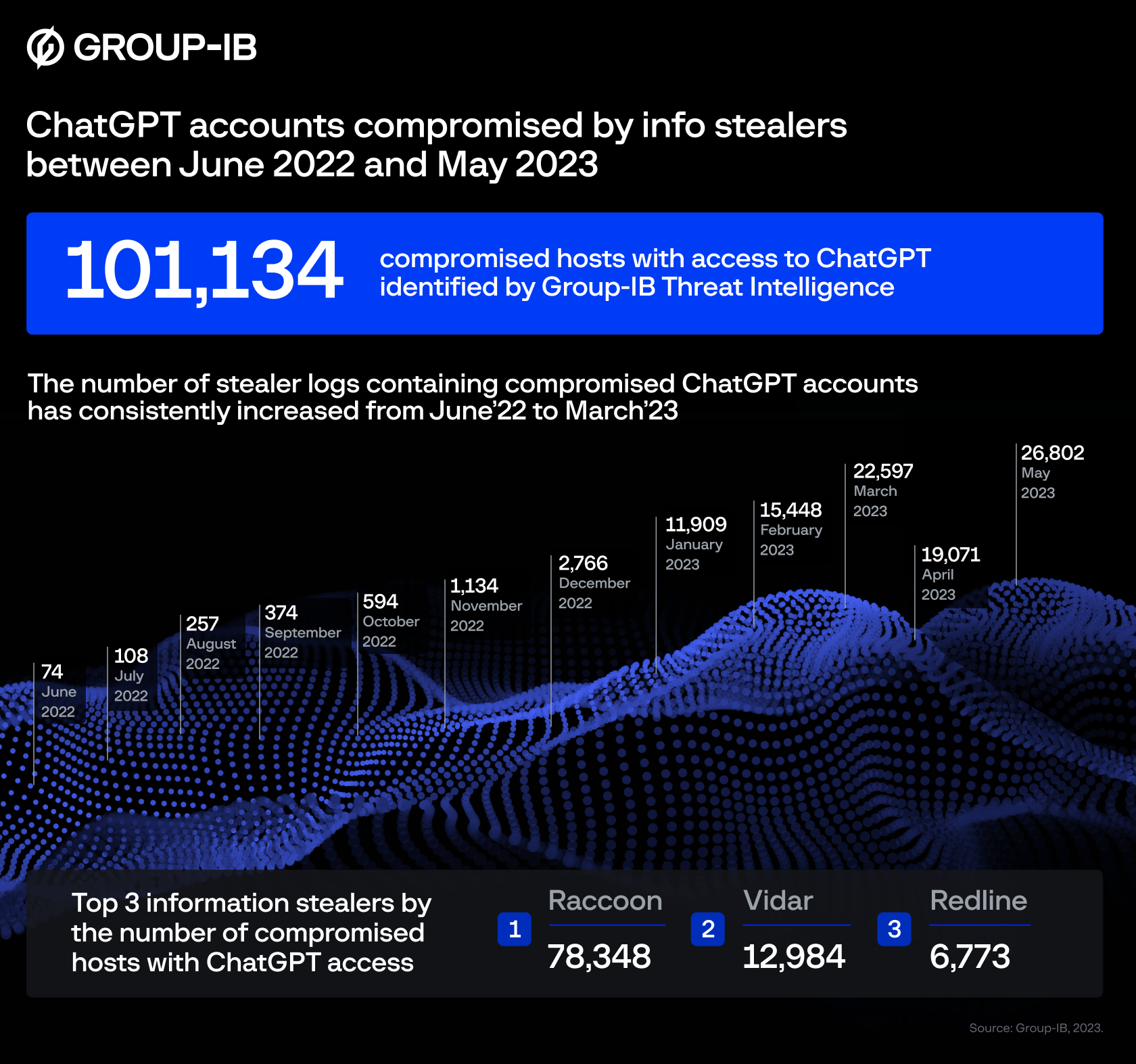
Global cybersecurity leader Group-IB has identified 101,134 infected devices with saved ChatGPT credentials. Throughout 2023, the company’s Threat Intelligence Platform found compromised account details in 26,802 malware logs traded on dark web marketplaces.
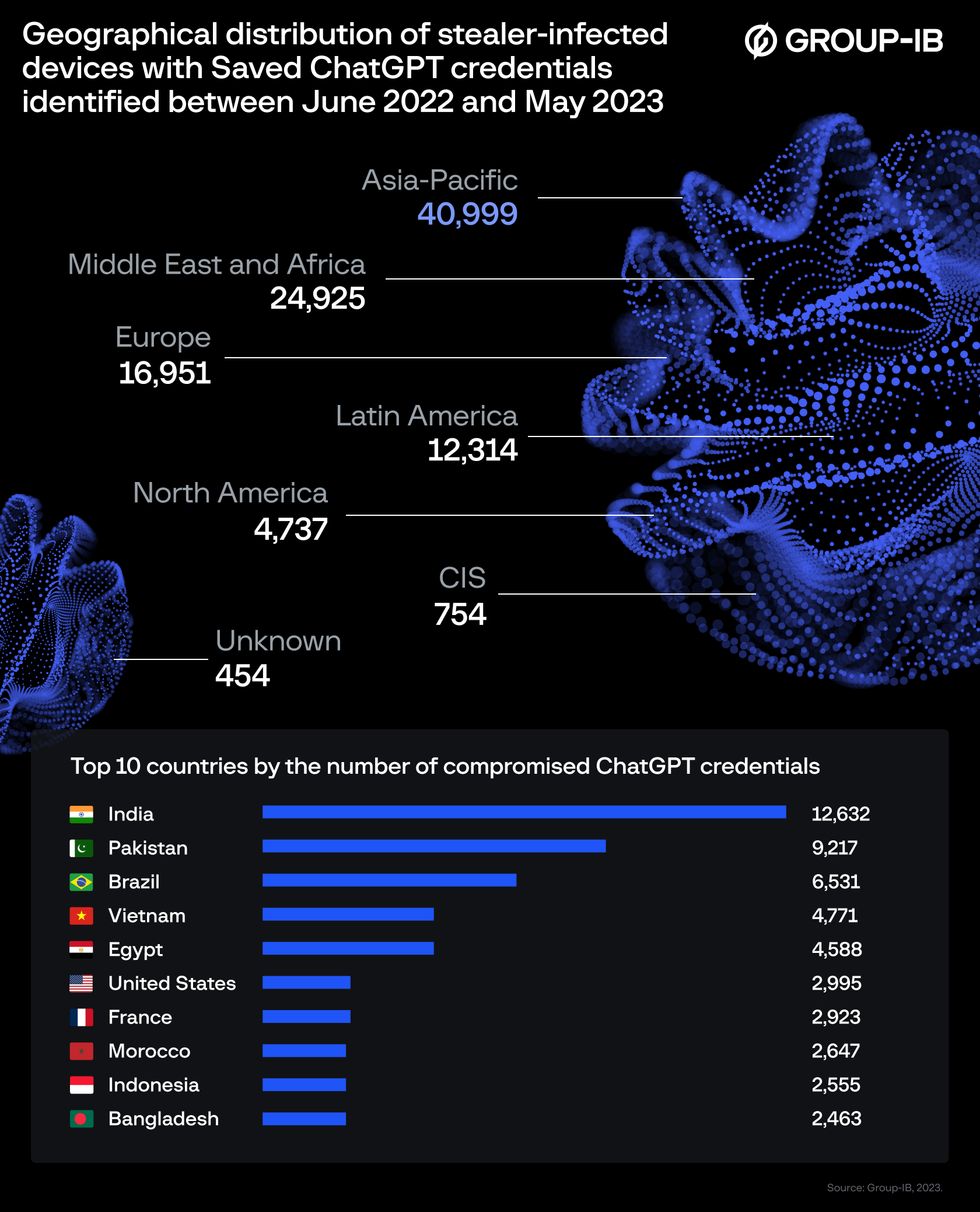
According to Group-IB’s findings, the Asia-Pacific region suffered the greatest concentration of ChatGPT credentials offered for sale, followed by the Middle East and Africa (MEA) region in second place.
Group-IB tech experts explained that when employees take advantage of ChatGPT to optimize business communications and marketing texts, the queries and responses are stored within the AI app. Consequently, any unauthorized access to a ChatGPT account could unearth a wealth of sensitive information.
Also Read: The Largest Data Breaches In The Middle East
Group-IB’s dark web analysis revealed that most compromised ChatGPT accounts were breached by a popular malware program known as “Raccoon Info Stealer”. The virus is often sent by email and can be used by hackers to gain access to sensitive data stored in internet browsers.
In the MENA area, accounts from users in Egypt, Morocco, Algeria, and Turkey topped the “most-infected” list, potentially exposing companies in the region to multiple threat actors.
“Many enterprises are integrating ChatGPT into their operational flow,” explained Dmitry Shestakov, Head of Threat Intelligence at Group-IB. “Employees enter classified correspondences or use the bot to optimize proprietary code. Given that ChatGPT’s standard configuration retains all conversations, this could inadvertently offer a trove of sensitive intelligence to threat actors if they obtain account credentials. At Group-IB, we continuously monitor underground communities to identify such accounts promptly”.
To mitigate the risks posed by compromised ChatGPT accounts, Group-IB suggests that users update passwords using current best practices while also implementing two-factor authentication.
News
At I/O 2026, Sundar Pichai Concedes AI Must Deliver Real Value
Gemini 3.5, a personal agent called Spark, agentic shopping, and Android XR eyewear are all aimed at making AI feel useful, not just impressive.
Google’s annual I/O developer conference (I/O 2026) has recently become a status update on the same question: can the company turn its AI spending into products people use every day? This year, chief executive Sundar Pichai described Google as being in a phase of hyper progress, while conceding this is the part of the cycle where people want to see real value in the products they use on a day-to-day basis.
The strategy on display was to push agents — AI systems that act on a user’s behalf — into nearly every Google product at once. Search now has an “intelligent search box” that returns generated explainer videos alongside links. Gmail, Docs, YouTube and Maps are gaining their own agent layers, including a Docs Live feature that turns spoken instructions into drafted text with citations.
Two new models, Gemini 3.5 and a cheaper Gemini 3.5 Flash, arrived the same day. Google says 900 million people now use Gemini, and that more than 50 billion images have been generated with it. The pricing tier names are likely to confuse buyers: a new AI Ultra plan launches at $100 a month, while the older Gemini AI Ultra drops from $250 to $200.
The flashier announcements were Gemini Omni, a video generator pitched as a more realistic answer to OpenAI’s discontinued Sora 2, and Gemini Spark, a personal agent that handles recurring tasks across a user’s Google account. A new universal shopping cart lets agents complete purchases across multiple retailers from inside Google itself, placing the company between the merchant and the buyer, and also owning the checkout.
Also Read: DJI Teases Dual-Camera Osmo Pocket 4P For 2026 Launch
Google also confirmed its Android XR eyewear, built with Samsung and frames from Warby Parker and Gentle Monster. Audio-only glasses ship this autumn; a display-equipped version, which would superimpose live translations into the wearer’s field of view, is still in development. Both sets translate, however only the display version shows you the result.
What Pichai did not resolve is the bargain underneath all this. An agent is only useful to the degree it knows your calendar, your inbox, your shopping history and your physical surroundings. Google has now confirmed that, in time, the same context may carry advertising.