News
Mimecast Releases Its CyberGraph AI Email Security Tool
If a malicious email message is detected, CyberGraph will display a color-coded contextual warning banner to warn the user and encourage them to take the right action.
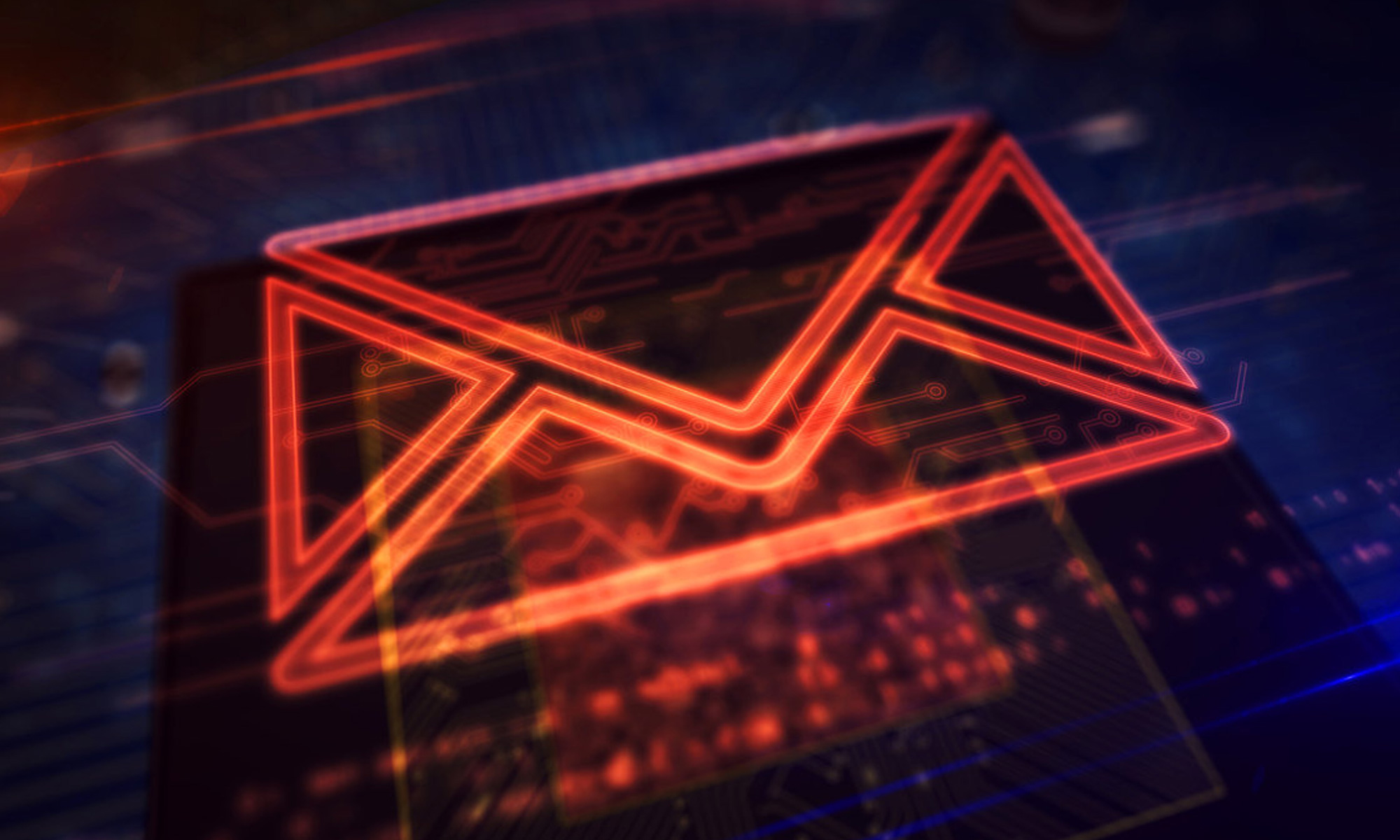
Since the outbreak of the COVID-19 pandemic forced many businesses around the Middle East to close their offices and abruptly transition to remote working, email phishing attacks have increased both in number and sophistication. This concerning new trend has put the topic of email security as a top priority for many businesses in the region.
According to Mimecast, a provider of cloud cybersecurity services for email, employees now click on three times as many malicious emails as they did before the term “social distancing” entered our collective lexicon.
Determined to better protect its customers against this growing threat, Mimecast has just launched a new artificial intelligence (AI)-enabled tool for email security, called CyberGraph. The tool promises to keep email phishing attacks at bay using machine learning algorithms capable of detecting anomalous behaviors that could be indicative of a malicious email.
“CyberGraph leverages our AI and machine learning technologies to help keep employees one step ahead with real-time warnings, directly at the point of risk,” explains Josh Douglas, threat intelligence lead at Mimecast. “Phishing and impersonation attacks are getting more sophisticated, personalized, and harder to stop. If not prevented, these attacks can have devastating results for an enterprise organization. Security controls need to be constantly updated and improved to outsmart threat actors,” he added.
Whenever CyberGraph determines an email message to be malicious, it displays a color-coded contextual warning banner to warn the user and encourage them to take the right action, such as mark the email as spam.
Also Read: Is Your Phone Hacked? How To Find Out & Protect Yourself
In addition to its ability to distinguish malicious email messages from legitimate ones, CyberGraph can also disarm trackers embedded in emails to keep unauthorized third parties from getting their hands on information that could be used to orchestrate highly targeted phishing attacks.
Like other cybersecurity solutions powered by machine learning algorithms, CyberGraph’s effectiveness will keep improving over time as more users adopt it to protect their inboxes.
News
At I/O 2026, Sundar Pichai Concedes AI Must Deliver Real Value
Gemini 3.5, a personal agent called Spark, agentic shopping, and Android XR eyewear are all aimed at making AI feel useful, not just impressive.
Google’s annual I/O developer conference (I/O 2026) has recently become a status update on the same question: can the company turn its AI spending into products people use every day? This year, chief executive Sundar Pichai described Google as being in a phase of hyper progress, while conceding this is the part of the cycle where people want to see real value in the products they use on a day-to-day basis.
The strategy on display was to push agents — AI systems that act on a user’s behalf — into nearly every Google product at once. Search now has an “intelligent search box” that returns generated explainer videos alongside links. Gmail, Docs, YouTube and Maps are gaining their own agent layers, including a Docs Live feature that turns spoken instructions into drafted text with citations.
Two new models, Gemini 3.5 and a cheaper Gemini 3.5 Flash, arrived the same day. Google says 900 million people now use Gemini, and that more than 50 billion images have been generated with it. The pricing tier names are likely to confuse buyers: a new AI Ultra plan launches at $100 a month, while the older Gemini AI Ultra drops from $250 to $200.
The flashier announcements were Gemini Omni, a video generator pitched as a more realistic answer to OpenAI’s discontinued Sora 2, and Gemini Spark, a personal agent that handles recurring tasks across a user’s Google account. A new universal shopping cart lets agents complete purchases across multiple retailers from inside Google itself, placing the company between the merchant and the buyer, and also owning the checkout.
Also Read: DJI Teases Dual-Camera Osmo Pocket 4P For 2026 Launch
Google also confirmed its Android XR eyewear, built with Samsung and frames from Warby Parker and Gentle Monster. Audio-only glasses ship this autumn; a display-equipped version, which would superimpose live translations into the wearer’s field of view, is still in development. Both sets translate, however only the display version shows you the result.
What Pichai did not resolve is the bargain underneath all this. An agent is only useful to the degree it knows your calendar, your inbox, your shopping history and your physical surroundings. Google has now confirmed that, in time, the same context may carry advertising.