News
How To Install Google Play Store On Windows 11 Right Now
The whole process takes roughly half an hour from start to finish, and it involves 7 simple steps.
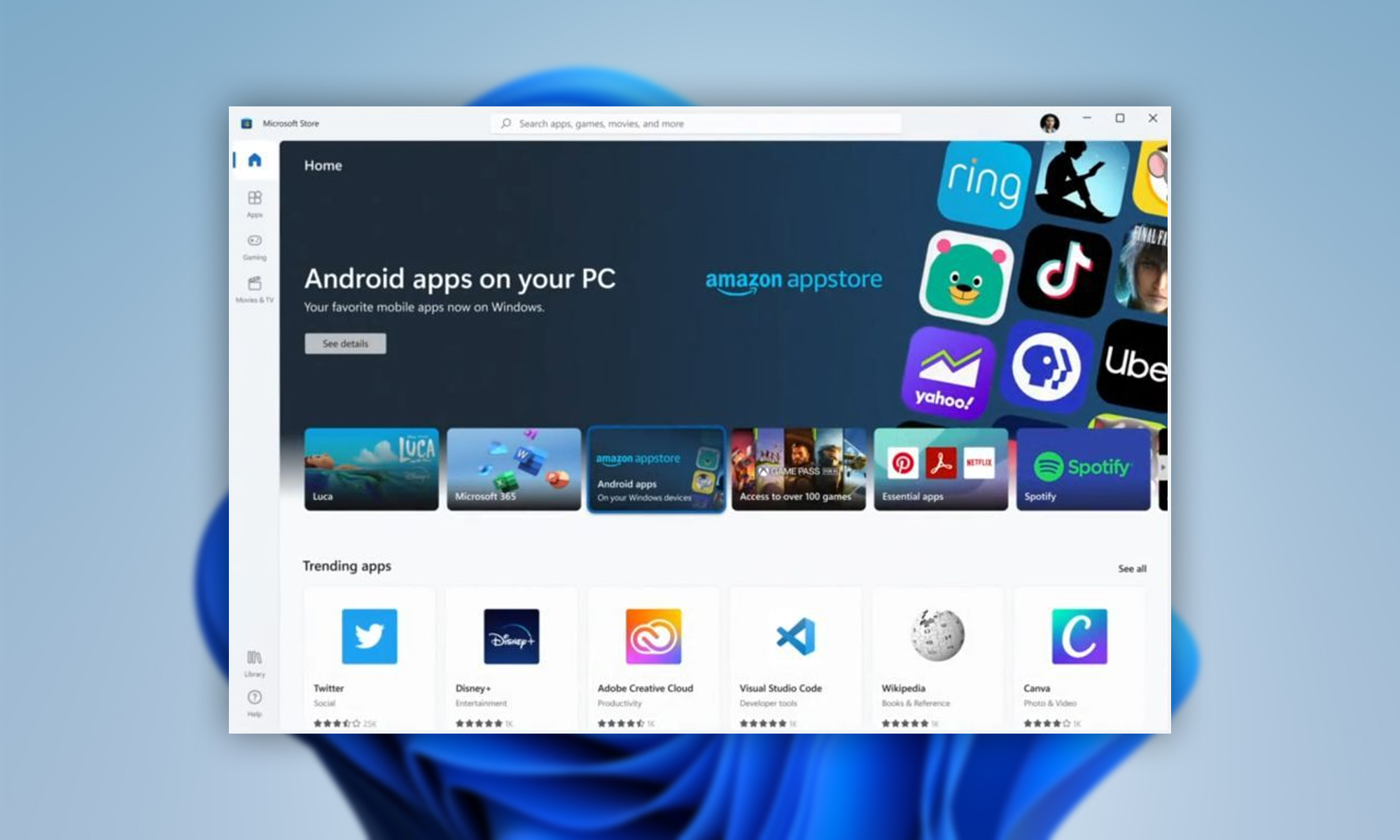
Last week, Microsoft launched the first version of Windows Subsystem for Android (WSA), whose purpose is to enable Windows users to launch Android apps alongside Windows apps. Unfortunately, the first version is limited to the Amazon Appstore and only a small number of early apps. Wanting more, an Italian UX design student using the nickname ADeltaX on the internet has figured out a way to install the Google Play Store on Windows 11, and he created a video guide and step-by-step instructions on his GitHub to make it easy for others to follow in his footsteps.
The whole process takes roughly half an hour from start to finish, and it involves the following steps:
- Download the Windows Subsystem for Android.
- Install the Windows Subsystem for Linux (yes, Linux).
- Install the unzip and lzip software packages.
- Download up-to-date Google Apps.
- Extract the Windows Subsystem for Android.
- Download, configure, and run the provided installation scripts to create a modified version of the Windows Subsystem for Android.
- Install the Windows Subsystem for Android using PowerShell.
From there, you can sign in to the Google Play Store and download any app or game. Just don’t expect everything to run smoothly because there’s a good reason why Microsoft is keeping the first version of WSA limited to a handful of hand-picked apps.
Also Read: Facebook Will Create 10,000 Jobs In The EU To Build Its Metaverse
If all this sounds like too much for something that might not even work properly, then you should know that there’s also a pretty straightforward way to install Android apps outside of the Amazon Appstore, and it revolves around a free tool called WSATools, which you can download from the Microsoft Store.
Just keep in mind that apps that depend on the Google Play Store won’t work using this method. Let us know if this guide helped you install Google Play Store on Windows 11.
News
DJI Teases Dual-Camera Osmo Pocket 4P For 2026 Launch
Though most technical claims for the new gimbal come from industry leaks rather than DJI’s own announcement.

DJI has teased a dual-camera version of its Osmo Pocket gimbal, confirming that the Osmo Pocket 4P will launch in 2026. The teaser image is the company’s first preview of the device, following months of speculation about a more advanced model in its pocket camera range.
The image shows a slightly larger device than the existing Osmo Pocket 4, with two camera modules mounted above a compact three-axis gimbal. Reports suggest one camera may use a 1-inch sensor paired with a wide-angle lens, while the second may carry a 3x zoom lens — though DJI has not officially confirmed any of these details.
According to leaks circulating ahead of the launch, the Osmo Pocket 4P could support 4K video at up to 240 frames per second, offer 14 stops of dynamic range and include 10-bit D-Log color support. Those features are commonly used by filmmakers who require greater flexibility during color grading and post-production. Reports also point to Hasselblad color tuning, continuing a partnership that has already appeared in some of DJI’s drone cameras, along with up to 128GB of built-in storage that would reduce reliance on external memory cards during longer shoots.
Also Read: AltoVolo Releases Sigma Footage & Sets Date For Demonstrator
The device is expected to retain features from the existing Osmo Pocket 4, including a three-axis mechanical gimbal, updated ActiveTrack subject tracking and a flip-out touchscreen display. The Osmo Pocket line is aimed at content creators, vloggers, and independent filmmakers seeking compact equipment that can produce usable footage without a larger camera system.
DJI has not provided pricing or a specific launch date beyond the 2026 window. Industry observers expect the Osmo Pocket 4P to cost more than the standard Pocket 4 because of the dual-camera setup and expanded recording capabilities, though no figures have been disclosed. So far, most of the technical detail circulating around the product remains tied to leaks rather than official confirmation.